Introduction
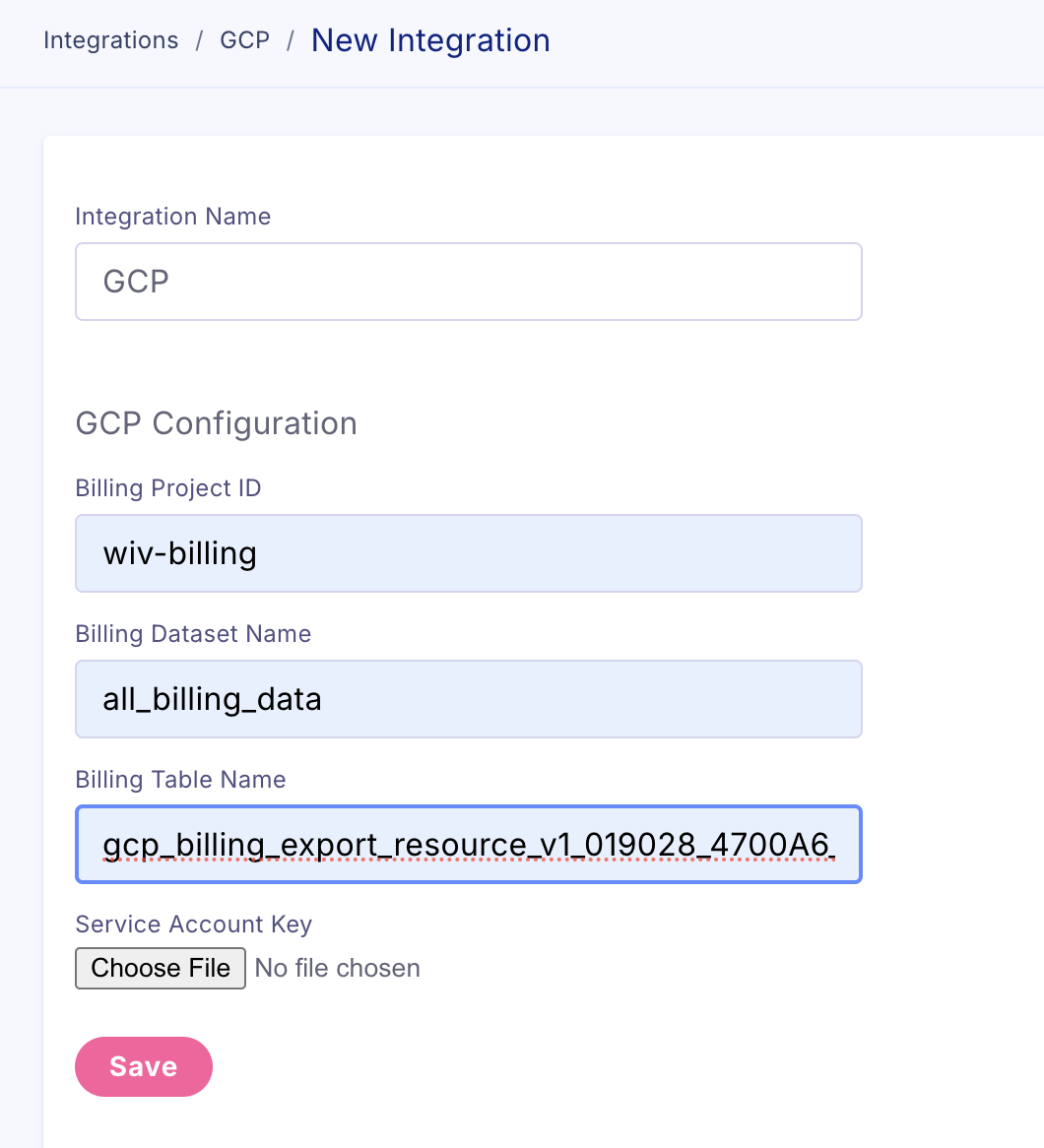
This documentation provides a comprehensive guide to onboarding a GCP account to Wiv using a script that automates the creation of a service account, the generation of a service account key, and the assignment of predefined roles to the service account at either the organization or project level.Prerequisites
1. BigQuery Cloud Billing Data Export
If you don’t have it, please follow this guide. Choose “Detailed usage cost data”.2. Required Permissions
The user running this script needs the following permissions: For Standalone Project setup:resourcemanager.projects.create(or use an existing project)serviceusage.services.enableon the target projectiam.serviceAccounts.createon the target projectiam.serviceAccounts.keys.createon the target projectresourcemanager.projects.setIamPolicyon the target projectserviceusage.quotas.updateon the target project (for BigQuery quota limits)
resourcemanager.organizations.getresourcemanager.organizations.getIamPolicyresourcemanager.organizations.setIamPolicy
| Scope | Role | Purpose |
|---|---|---|
| Organization | roles/resourcemanager.organizationAdmin | List orgs, set org-level IAM |
| Project | roles/owner or roles/editor | Create resources, enable APIs |
| Project | roles/iam.serviceAccountAdmin | Create service account and keys |
| Project | roles/serviceusage.serviceUsageAdmin | Enable APIs |
| Project | roles/serviceusage.quotaAdmin | Set BigQuery quota limits |
If you don’t have organization-level permissions, the script will automatically fall back to standalone project mode.
Step-by-Step Guide
1. Login to GCP
Open GCP Cloud Shell with the onboarding repo: https://shell.cloud.google.com/cloudshell/editor?cloudshell_git_repo=https://github.com/wiv-ai/GCPOnBoarding.git2. Run the Script
Start the script by executing:3. Login to GCP
The script will prompt you to log in to Google Cloud using the gcloud auth login command. Follow the instructions in your terminal to authenticate.4. Select Configuration Type
The script will ask if you want to set up for a standalone project or an entire organization:- Standalone Project: Permissions will be set at the project level.
- Entire Organization: If you choose to set permissions at the organization level, the script will fetch a list of organizations available to you. If there are multiple organizations, you will be prompted to select one.
5. Enter the Project ID for Service Account Creation
The script will prompt you for a GCP Project ID where the service account will be created:my-gcp-project.
6. API Enablement
The script will enable the following APIs on the specified project:- recommender.googleapis.com
- cloudresourcemanager.googleapis.com
- compute.googleapis.com
7. Service Account Creation
The script creates a new service account namedwiv-sa with the display name “Wiv Service Account.”
8. Generate Service Account Key
The script will generate a key for the service account and save it askey.json in the current directory. This key file is essential for applications or scripts that need to authenticate as the service account.
9. Assign IAM Roles
The script will assign the following IAM roles to the service account at either the organization or project level:- roles/recommender.computeViewer
- roles/recommender.viewer
- roles/monitoring.viewer
- roles/compute.viewer
- roles/bigquery.jobUser
- roles/recommender.bigQueryCapacityCommitmentsViewer
- roles/container.viewer
- roles/bigquery.dataViewer
- roles/cloudsql.viewer
- roles/run.viewer
- roles/cloudfunctions.viewer
- roles/pubsub.viewer
- roles/spanner.viewer
- roles/logging.viewer
- roles/iam.securityReviewer
- roles/compute.networkViewer
- roles/cloudbuild.builds.viewer
- roles/dataflow.viewer
- roles/redis.viewer
- roles/securitycenter.viewer
- roles/cloudkms.viewer
- roles/artifactregistry.reader
- roles/gkebackup.viewer
- roles/cloudasset.viewer
- roles/bigquery.resourceViewer
For a detailed mapping and explanation of the required GCP permissions and their usage, please refer to the GCP permissions list.
10. Completion
After the script finishes running, you’ll see a completion message confirming that the service account has been created and configured:Verify Permissions
After running the script, verify that the service account has been created and the roles have been assigned correctly in the GCP Console IAM & Admin section.Additional Notes
- Error Handling: If any step fails, the script will print an error message indicating the issue and exit. Check the error message to identify what needs to be corrected (e.g., insufficient permissions or an incorrect project ID).
- Security: Keep
key.jsonsecure as it contains sensitive information. You may want to move it to a safe location or restrict its permissions after the script completes.
Example Output
Here’s a sample output for a user who chose to apply permissions at the organization level:Ensure that you have the necessary permissions and understand the implications of assigning roles at the organization level. Misconfigurations can lead to security risks or unintended access to resources within your organization. Always follow the principle of least privilege when assigning roles.