Overview
Wiv is a high-performance FinOps platform built for real-time identification of cost-saving opportunities and anomalies. By securely integrating a Cross-Account IAM Role and AWS EventBridge, Wiv delivers a unique combination of deep visibility and instant responsiveness. This document details the security architecture and outlines the complete data scopes required to achieve maximum optimization.The Security Handshake & Guarantees
All connectivity strictly follows AWS best practices for third-party SaaS integration, ensuring maximum security and trust. Key Security Guarantees:- Metadata Focused: Operations concentrate on metadata scans to efficiently identify optimization opportunities.
- Real-Time Intelligence: Wiv utilizes EventBridge for instant reaction to account changes, eliminating the delay of waiting for daily billing updates.
- Encryption & Isolation: All sensitive connection metadata is stored exclusively within your account’s Secrets Manager and is never retained on Wiv’s side.
- No Customer Data Access: Wiv is architected to prevent access to PII, database records, or application-level data.
| Security Aspect | Detail |
|---|---|
| Metadata Focused | Operations primarily use metadata scans to pinpoint optimization opportunities. |
| Real-Time Intelligence | Wiv uses EventBridge to react instantly to account changes, eliminating the wait for daily billing updates. |
| Encryption & Isolation | All sensitive connection metadata is securely stored within your account’s Secrets Manager and is never persisted on Wiv’s side. |
| No Customer Data Access | Wiv is explicitly prevented from accessing PII, database records, or application-level data. |
Visual Architecture Flow
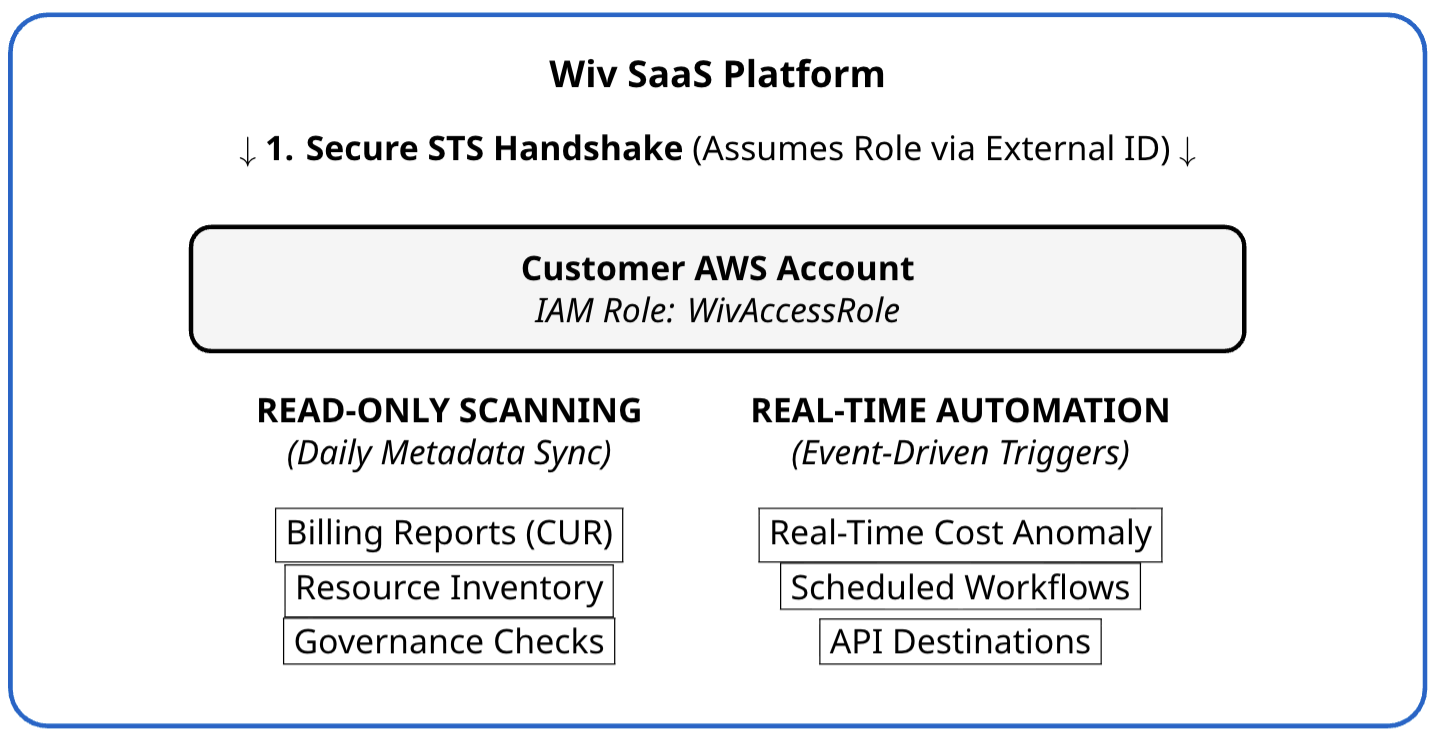
Wiv’s Event-Driven FinOps: Real-Time Value and Permission Framework
The Strategic Value of Real-Time Triggers (AWS EventBridge)
Wiv’s core architecture leverages Event-Driven Responsiveness, distinguishing it from traditional FinOps tools that rely on slow, periodic polling. This design enables Wiv to capture infrastructure changes instantly as they happen.- Why Real-Time is Essential: Delays, such as waiting 24 hours for a billing report, can result in thousands of dollars in wasted spending due to misconfigured, expensive resources. Real-time triggers allow Wiv to immediately identify, alert on, and prevent these costly anomalies.
- Mechanism: Wiv uses AWS EventBridge Rules, configuring them to “listen” for specific lifecycle events that impact cost (e.g., changes in EC2 state, creation of a new RDS instance, or activation of Billing Alarms).
- Secure Data Flow: When an EventBridge rule is triggered, it securely invokes an API Destination. This pushes the necessary metadata to Wiv’s backend for immediate processing.
Permission Matrix: Detailed Overview
The comprehensive table below details all API actions granted to the WivAccessRole, categorized by functional domain. These permissions are primarily read-only, supporting deep analytical capabilities.| Service Domain | Allowed API Actions |
|---|---|
| FinOps & Billing | ce:Get*, ce:List*, ce:Describe*, ce:CreateAnomalySubscription, cur:Get*, billing:Get*, consolidatedbilling:Get*, consolidatedbilling:List*, invoicing:List*, payments:Get*, payments:List*, tax:Get*, tax:List* |
| Compute & EC2 | ec2:Describe*, ebs:List*, autoscaling:Describe*, compute-optimizer:Get*, compute-optimizer:Describe*, lambda:ListFunctions, lambda:ListProvisionedConcurrencyConfigs, lambda:ListTags |
| Databases | rds:Describe*, rds:List*, dynamodb:Describe*, dynamodb:ListTables, dynamodb:ListTagsOfResource, elasticache:Describe*, elasticache:List*, redshift:Describe* |
| Storage & S3 | s3:Describe*, s3:List*, s3:GetAccelerateConfiguration, s3:GetBucketVersioning, s3:GetLifecycleConfiguration, backup:List*, fsx:Describe*, fsx:List*, elasticfilesystem:Describe*, elasticfilesystem:List* |
| Containers (K8s) | eks:DescribeCluster, eks:List*, ecs:Describe*, ecs:List*, ecr:Describe*, ecr:List* |
| Networking & CDN | cloudfront:Get*, cloudfront:List*, elasticloadbalancing:Describe*, route53:ListHostedZones, route53:ListHostedZonesByName, route53:ListResourceRecordSets |
| Modern Stack & AI | athena:StartQueryExecution, athena:GetQueryResults, glue:*, sagemaker:List*, sagemaker:Describe*, bedrock:InvokeModel, kafka:Describe*, kafka:List*, es:Describe*, es:List* |
| Governance & IAM | cloudtrail:Describe*, cloudtrail:Get*, cloudtrail:List*, cloudtrail:LookupEvents, config:Describe*, config:Get*, config:List*, iam:ListAccountAliases, organizations:DescribeOrganization, organizations:ListAccounts |
| Optimization Checks | trustedadvisor:Describe*, trustedadvisor:Get*, trustedadvisor:List*, trustedadvisor:RefreshCheck, trustedadvisor:GenerateReport, support:Describe*, support:DescribeTrustedAdvisorChecks, support:RefreshTrustedAdvisorCheck, savingsplans:DescribeSavingsPlansOfferings |
| Automation (Write) | events:PutRule, events:PutTargets, events:CreateApiDestination, events:CreateConnection, events:InvokeApiDestination, events:DeleteRule, secretsmanager:*, iam:PassRole, iam:PutRolePolicy, iam:CreateServiceLinkedRole |
Deep-Dive: Necessary Automation and Write Permissions
To facilitate the real-time, event-driven workflows, Wiv requires a precise and surgical set of “Write” permissions. These actions are strictly limited to managing the necessary Wiv-related infrastructure within your account for secure, real-time data integration.| Permission | Purpose |
|---|---|
events:PutRule | Creates EventBridge rules to listen for specific, cost-impacting resource changes and lifecycle events in real-time. |
events:PutTargets | Links the newly created rules to Wiv’s API endpoints, ensuring event data is correctly routed to our platform upon trigger. |
events:CreateApiDestination | Establishes a secure HTTPS gateway within your environment, used to transmit metadata events back to the Wiv engine for immediate analysis. |
secretsmanager:CreateSecret | Used by Wiv to store sensitive API tokens required for EventBridge connections within your AWS Secrets Manager, ensuring credentials remain encrypted and within your security boundary. |
iam:PassRole | Allows the EventBridge service to securely utilize the permissions defined in the WivAccessRole when executing its triggers and delivering data. |
iam:PutRolePolicy | Enables Wiv to update its internal automation policies (e.g., as new AWS services or optimization triggers are introduced) without requiring manual administrative overhead. |